Ransomware has hit the headlines throughout 2022 as cybercriminals launched audacious attacks against major targets and made record-breaking ransom demands.
Ransomware has hit the headlines throughout 2022 as cybercriminals launched audacious attacks against major targets and made record-breaking ransom demands.
In October, Jeremy Fleming, director of GCHQ, revealed that the number of ransomware attacks on British institutions has doubled in the past year.
He said: “We’ve seen twice as many attacks this year as last year in the UK – it is because it works. It just pays. Criminals are making very good money from it and are often feeling that that’s largely uncontested.”
The National Cyber Security Centre also announced that it has tackled a record-breaking number of incidents in 2021, with ransomware attacks from Russia “dominating” its work. On the continent, ENISNA, the European Union Agency for Cybersecurity, warned that ransomware is the ‘prime threat’ faced by organisations today and said it had observed a 150% rise in ransomware attacks.
Unfortunately, ransomware is here to stay, which means organisations must be constantly vigilant. To help you understand the threat, here are some of the biggest trends from 2021 and predictions for 2022.
Mid-Game Hunting Ransomware Gangs
A few years ago, the industry was talking about big-game ransomware, which referred to hackers going after large companies that could afford to pay out huge sums of money.
This year, more and more hackers have been going after small or mid-sized companies who lack financial resources to pay large ransoms – or fund a large SOC. One study suggested that the number of cyberattacks against mid-sized businesses in every industry soared by more than 50%.
In 2021, the average ransom payout by a mid-sized organisation was $170,404, according to Sophos.
“Ransomware actors adjust their ransom demand in line with their victim’s ability to pay, typically accepting lower payments from smaller companies,” it wrote.
“The data backs this up, with the average ransom payment for 100-1,000 employee organisations coming in at US$107,694, while the average ransom paid by 1,000 to 5,000 employee organisations was US$225,588.”
Unfortunately, the mid-market is now an outsized target for ransomware gangs.
Record-Breaking Ransom Demands
Despite the rise of mid-game hunting ransomware gangs, some hackers still seem to live by the motto: “Go big, or go home.”
This year, we saw the largest ransomware demands ever made – along with an overall rise in the amount of money paid by victims.
The average ransom paid by companies has increased by 82% to $570,000 in the first half of 2021, according to data from Palo Alto Networks’ security consulting team, Unit 42. That is the highest level ever recorded.
At the beginning of the year, the largest ever ransom demand was $30million, but that record was broken first in March when Acer was hit by a $50 million ransom note and then again in July when hackers asked for $70 million to halt the Kaseya attack.
In the US, investigators claimed crypto wallets linked to the 10 most common ransomware variants were involved in transactions worth $5.2 billion, showing just how much money is being made in the ransomware sector.
Personalised Ransomware
A study from Sophos found that the number of companies that reported suffering a ransomware attack has actually declined from 54% in 2017 to 37% in 2021. This means that criminals have moved away from a ‘spray and pray’ approach in favour of launching targeted attacks that are designed with specific targets in mind.
“The number of attacks could be due in part to evolving attack approaches,” Sophos wrote. “For instance, many attackers have moved from larger scale, generic, automated attacks to more targeted attacks that include human-operated, hands-on-keyboard hacking. While the overall number of attacks is lower, our experience shows that the potential for damage from these targeted attacks is much higher.”
Zero Days and New Strains of Ransomware
As the ransomware gangs earn more money, they are able to step up their operations. This has resulted in an explosion of zero-days, with businesses facing new strains of ransomware.
One survey of managed security service providers (MSSPs) found that 74% of threats that their customers experienced were zero-day malware strains that signature-based solutions could not detect when first encountered.
At least 66 zero-days have been found in use this year, according to the MIT Technology Review. That is a record-breaking number, which caps off a year that has seen many ransomware records smashed.
Pandemic Phishing
The coronavirus presented a huge opportunity to cybercriminals because it gave them new and easy ways to target their victims. KPMG was one of many analysts which warned of criminals using “Covid-19 themed lures for phishing” which “exploit your consumers’ and employees’ concerns over the pandemic and the safety of their loved ones”. Phishing is one of the main tools used by ransomware gangs, who only need to persuade one person to click on a malicious email to cause an infection.
These lures include false offers of in-demand products like masks, vaccines, hand sanitiser and even toilet paper. We know that attackers are always looking for ways to penetrate company networks. The security enjoyed by large enterprises (and Censornet customers that benefit from the joined-up protection offered by our autonomous integrated cloud security platform) makes it difficult for attackers to launch full-frontal assaults. But large, medium and small-sized organisations all share the same soft, vulnerable underbelly: humans.
Phishers prey on fear and emotion so will use every cynical tactic they can think of to manipulate their victims. The solution is a security platform in which products like email, web and cloud security work together to provide full-spectrum protection against multi-channel attacks. And, of course, human training. If your staff know how to spot a phishing email, they are less likely to fall for it.
Predictions for 2022:
Autonomous Security Takes Centre Stage
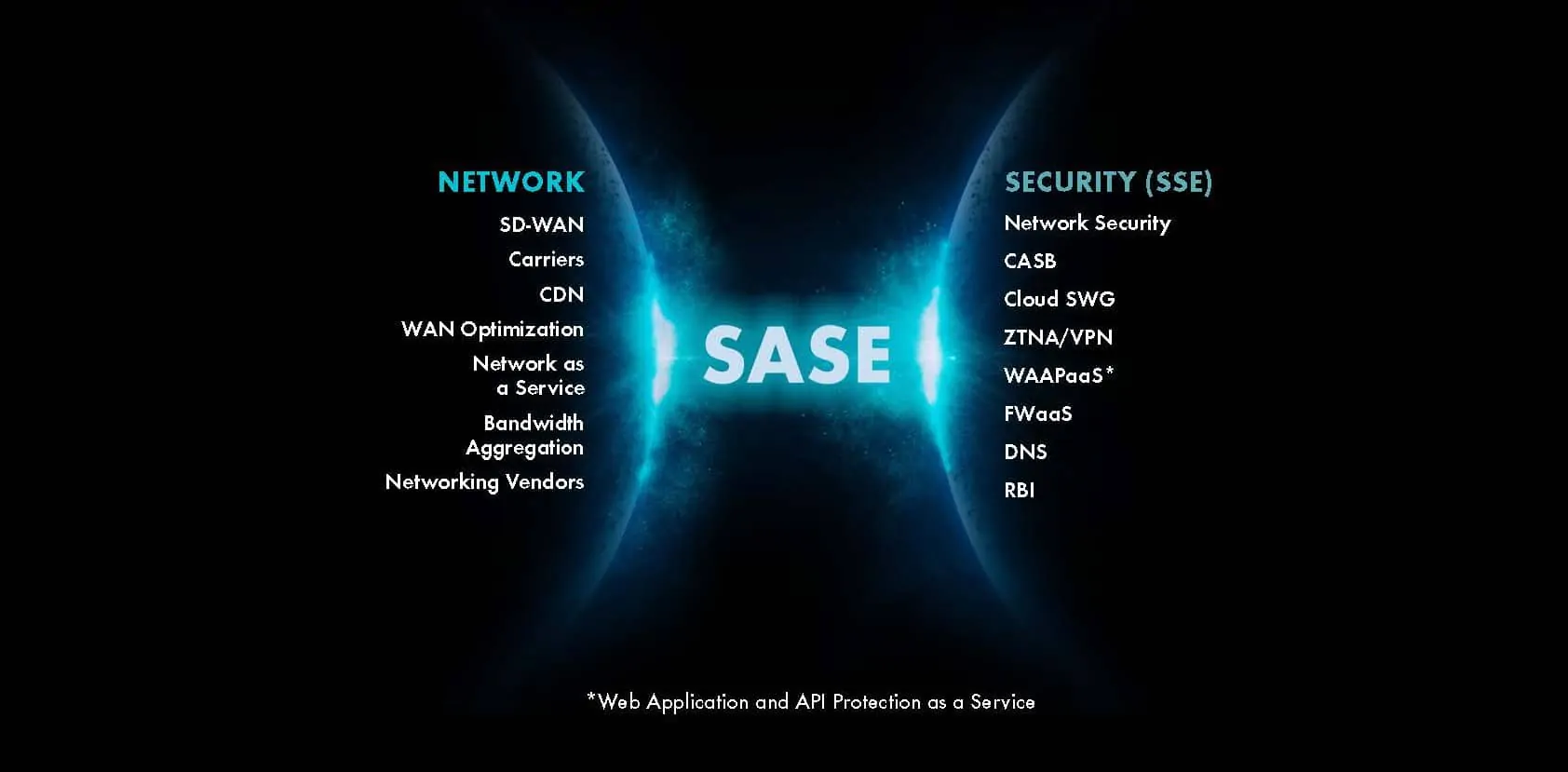
Automated security systems can be useful when it comes to dealing with the “known knowns”. They can perform routine tasks at a speed no human could ever manage, helping to liberate overworked SOC staff from dull, time-consuming manual work and alleviating alert fatigue.
But the next step is autonomous security which is capable of working without human intervention to deal with unknown threats and triage security incidents which require intervention from security teams.
Autonomy is the future of cybersecurity, so we expect to see autonomous cybersecurity solutions play an increasingly important role in the battle against ransomware during 2022.
Enforcement Strikes Back
After the Colonial Pipeline incident, investigators managed to retrieve $2.3 million in Bitcoins paid to the DarkSide ransomware gang.
Bitcoin has a reputation for being untraceable which is mostly, if not entirely, unearned. In 2022, we expect to see law enforcement strike back against ransomware gangs by tracing and confiscating their ill-gotten gains.
More Record-Breaking Ransom Demands
Criminals made some audacious demands in 2022 and they are not likely to dial back their requests.
Ransoms should be expected to get even bigger next year, particularly if hackers succeed in targeting companies or national infrastructure.
Small and mid-sized companies are also likely to be forced into paying more and more ransoms. We expect mid-market companies to continue being a major target for ransomware gangs, so expect attacks to increase.
Platforms Step Up
We know that enterprise-grade security has always been the preserve of large, rich companies. But this is changing. Today, companies like Censornet offer platforms which incorporate a range of cybersecurity solutions that protect across web, email, cloud and other channels.
As the mid-market faces more and more ransomware attacks, companies will need to step up their defences. Platforms are the best way to do this, offering the protection enjoyed by enterprises at a fraction of the cost.
There is power in an autonomous integrated security platform: Find out why here.