Imagine receiving an email that looks official, complete with logos and a seemingly legitimate request. You’re prompted to scan a QR code to ‘enhance your security’. It’s a scenario many faced in the third quarter of 2023, as cybercriminals unleashed a wave of QRishing attacks.
In today’s digital landscape, Microsoft 365 has become an integral part of many organisations, streamlining operations and fostering collaboration. However, its ubiquity has also made it a prime target for cybercriminals, with phishing being one of the most prevalent threats.
What is QRishing?
Traditional phishing methods have been around for years, but cybercriminals are always looking for innovative ways to deceive their targets. Enter QRishing, a sophisticated form of phishing that leverages QR codes. These attacks are meticulously crafted, often impersonating trusted entities. The unsuspecting user, believing they are taking a security measure, scans the QR code. This action can lead them to a malicious site designed to harvest credentials, deploy malware, or even gain control over the user’s device.
Why Microsoft 365?
Microsoft 365’s widespread adoption makes it a lucrative target. In fact, Microsoft holds the title as the most impersonated corporate brand. With its suite of interconnected tools and vast user base, it offers cybercriminals a rich environment to exploit. A successful breach can provide these malicious actors with access to a wealth of data, from corporate communications to sensitive business documents. Moreover, the interconnected nature of Microsoft 365’s suite of tools means that compromising one component can potentially provide a pathway to others, amplifying the potential damage.
It’s not only the brand name attracting cybercriminals. It’s the holes in the solutions too – Microsoft’s email security is notoriously patchy. Just this year, The Verge posted an article calling out Microsoft “for ‘blatantly negligent’ cybersecurity practices” with Tenable’s CEO saying Microsoft’s cybersecurity track record is “even worse than you think”. In recent testing, Microsoft 365 was compared to Censornet to measure delivery rates of real-world Spam campaigns. Microsoft rejected 3.3% of content vs. 95% by Censornet.
The Human Element
Despite security holes, the success of phishing attacks often hinges on exploiting human psychology. Cybercriminals bank on the fact that a well-crafted phishing email can deceive even the most vigilant user. This makes continuous education and awareness crucial.
Employees need to be equipped with the knowledge to identify and report potential phishing attempts. Regular training sessions, simulated phishing exercises, and awareness campaigns can go a long way in bolstering an organisation’s first line of defence.
Beyond Native Defences
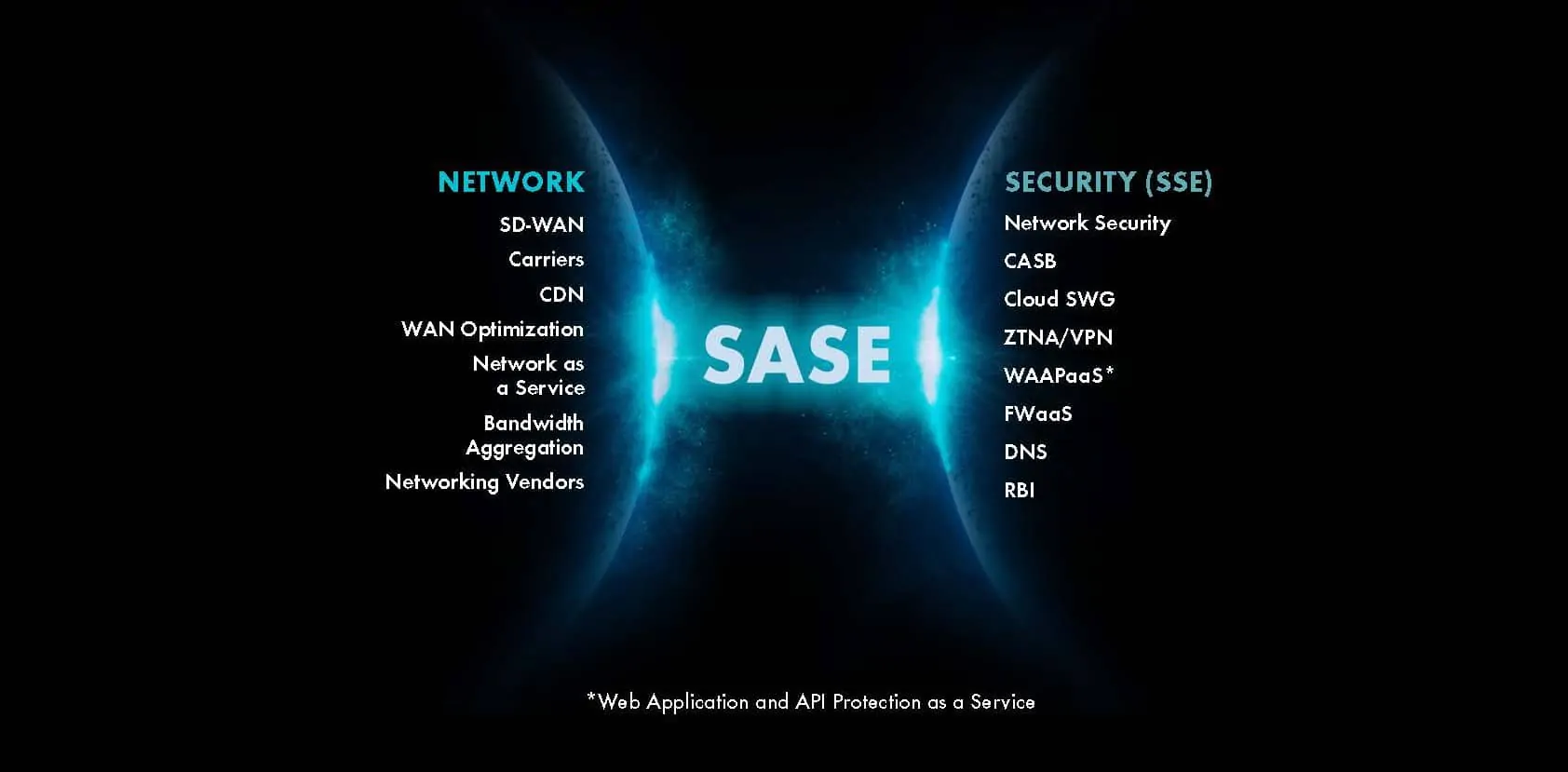
While Microsoft 365 offers a suite of security features, the evolving nature of cyber threats means that relying solely on these native defences can leave organisations vulnerable. The gaps in Microsoft’s email security underscore the importance of adopting additional, robust security measures.
Integrated security solutions, which provide comprehensive coverage across email, web, and cloud channels, are essential in today’s threat landscape. Such solutions not only detect and mitigate threats in real-time but also offer insights and analytics to inform and refine an organisation’s security strategy. By adopting a multi-layered approach, organisations can ensure that they are well-equipped to defend against the ever-growing and ever-evolving cyber threats of the modern age.
The Role of Advanced threat detection
While the human element is a significant factor in the success of phishing attacks, technology plays a pivotal role in bolstering an organisation’s defences. Advanced threat detection, real-time monitoring, and machine learning algorithms can identify and block phishing attempts before they reach the end-user. Furthermore, automated incident response can help mitigate the impact of any successful attacks, ensuring rapid containment and recovery.
The digital age, with its myriad of opportunities, also brings with it a host of challenges. As organisations continue to embrace tools like Microsoft 365, they must also be cognisant of the associated risks. Phishing, in its various forms, remains a significant threat, and a proactive, multi-faceted defence strategy is imperative.
For those looking to delve deeper into securing their Microsoft 365 environment and understanding the nuances of today’s threat landscape, download our comprehensive guide here. This guide provides actionable insights and best practices to fortify your organisation’s digital defences.