Remote working security refers to the practice of using technology and security measures to enable employees to work remotely in a secure and efficient manner. This typically involves providing employees with access to the necessary tools and resources, such as secure networks and communication channels, as well as implementing security measures to protect against cyber threats.
Automatically defend against the newest forms of multi-channel and cross-channel attacks, stopping them in their tracks before any damage is caused to your organisation. Censornet’s single cloud platform gives you end-to-end attack visibility and protection for your workers, wherever they are in the world.
✔ End-to-end attack visibility and protection
✔ Account Takeover protection
✔ Advanced Phishing and CEO Fraud prevention


With the remote workforce now outside the perimeter, it’s crucial to have extra visibility into all cloud applications that are being used, whether that use is approved or not. With fast and flexible deployment, the Censornet Platform protects your users, wherever they are.
✔ Total discovery and visibility of sanctioned and un-sanctioned cloud apps
✔ Visibility and protection at every stage of an attack
✔ Flexible deployment with agents, gateways or both, with centralised policy management
With the flexibility of remote working comes the risk of losing data and control. With unrivalled insight into users, the ability to manage access and activity on a granular level, and data security across all services – Censornet provide the ability to secure and manage your data, avoiding data sprawl and protecting the modern workforce.
✔ Managing business processes and workflows across all major cloud apps
✔ Total control over where your data goes


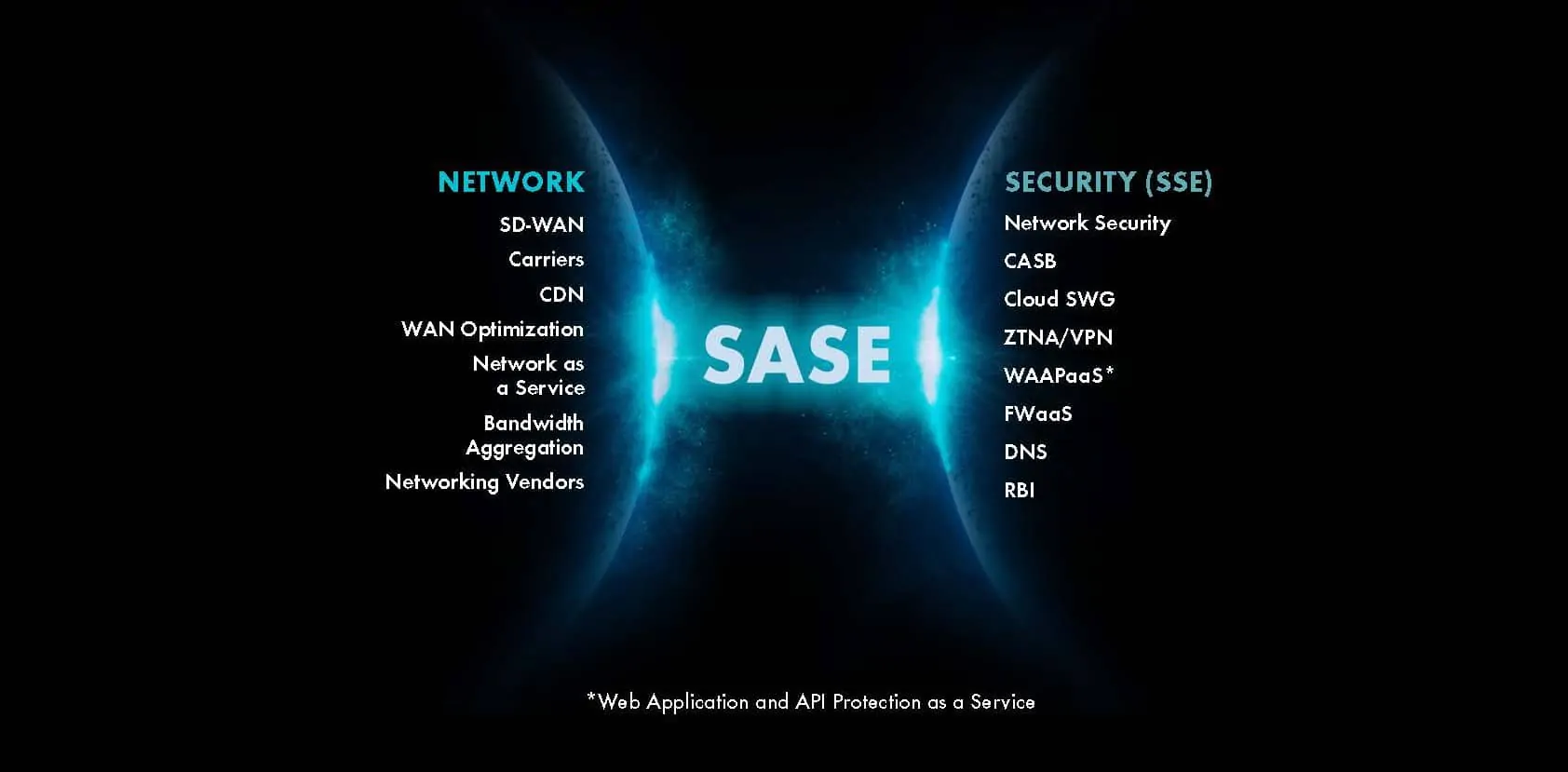
The traditional safety of the corporate perimeter and its firewall aren’t sufficient to support a newly distributed workforce. An entirely new perimeter built on identity and context is needed and prerequisite to the adoption of Zero Trust Network Access (ZTNA) – the first stop for many organisations on the journey to Secure Access Service Edge (SASE).
✔ Identity and context are the new perimeter
✔ Fully integrated with AD and/or Azure AD
The unique, underlying architecture, of the Censornet Platform, combines threat protection, with performance to deliver an unrivalled user experience.
✔ Smooth audio and video calling
✔ Fast uploads/downloads
✔ Ultra-fast response times
✔ Support for split tunnelling (simultaneous direct-to-Internet and VPN connections) * *compared to proxy or cloud proxy-based solutions

Contact us today to discuss how Censornet can help secure your remote working environment. One of our specialists can guide you through our Remote Health Check and answer any queries you may have.
Protect your remote workforce, secure your business with Censornet’s single cloud platform





If you wish to chat to someone about our products or services please contact our UK office on the number below:
0845 230 9590
Adding {{itemName}} to cart
Added {{itemName}} to cart