The death of the traditional perimeter and the ubiquity of cloud-first systems mean that cyber threats are no longer confined to one particular attack vector.
In an attempt to handle attacks from all sides, mid-market firms typically use an average of 24 point products to protect themselves. But between each point solution is a security gap that cybercriminals can exploit. According to Verizon, 94% of security incidents begin with a malicious email, with 65% of these turning into cross-channel attacks.
Yet only 37% of the mid-market can protect themselves from these cross-channel attacks – If a threat gets past or between one of those 24 point products, the majority of companies are at serious risk of a more costly breach. If your endpoint solutions are siloed from each other, once an attack evades one defence – whether it’s email, cloud, web, or identity – it’s highly unlikely to be stopped by others.
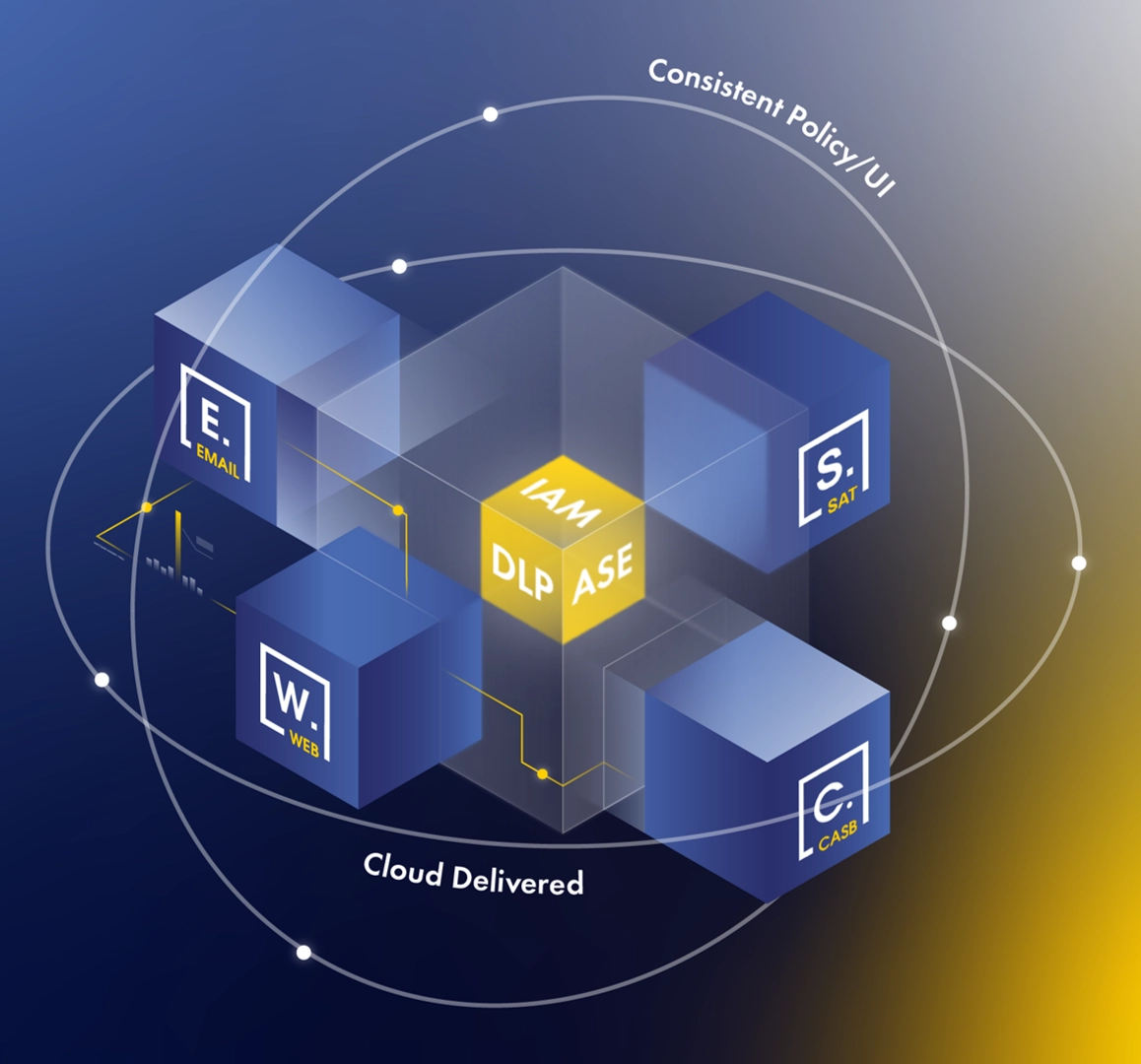
This is the backdrop to the growing trend for joined-up security models. The more closely connected your security systems are, the fewer gaps you present for cyberattacks to exploit. One way to achieve this joined-up state is to attempt to integrate your point products – manually plumbing them together so they can share data and work in concert. The other is to consolidate those products in a single platform – so they’re connected as standard, share data, act autonomously and are part of the same platform from the same vendor.
Integrate or consolidate?
A consolidated approach comes with plenty of benefits. By delivering email, web and cloud application security with identity and context all within the same package, organisations can reduce the vulnerabilities that sit between and across major attack surfaces.
However, consolidation isn’t foolproof: though you may have consolidated to one or several vendors, each may provide tools that might not be as tightly integrated as you need. As a result, choice of provider is important – otherwise, you may end up with multiple different identity stores and consoles that you’ve got to log into to manage the individual point products, even though you’ve undertaken a huge consolidation.
In short, whilst consolidating to a single vendor is obviously important, that only works if that vendor’s products are very tightly integrated and talk to one another autonomously. Otherwise, you’re still going to have gaps, which attackers will find – and target.
Integration means that the products you have consolidated seamlessly share data across your security infrastructure. The various security products should be simpler to use and manage (all from one platform), and reduce the need for manual intervention. That’s not to mention the ease of reporting, transparency on all incoming threats, and the ability to have a holistic view of your entire security posture in one place. An integrated approach also means threat intelligence can be shared faster, so new threats are spotted more quickly.
The way to the future: SASE and XDR
A more integrated approach to security also paves the way for emerging models like secure access service edge (SASE) and extended detection and response (XDR). SASE allows for rapid, flexible security at the edge of the network, with authentication following the user, based on contextual data rather than weak login credentials. XDR allows for autonomous collection and correlation of data from multiple security systems, enabling faster detection of threats and improved investigation and response times through rapid analysis.
 These kinds of distributed, intelligent, and autonomous abilities are essential as threats become more complex and working practices become more spread-out. According to Gartner, 89% of organizations want SASE and XDR to work together, either by consolidating into a single provider (43%) or keeping them distinct but integrated (46%). Keeping SASE and XDR distinct from one another enables a balance of best-of-breed functionality while maintaining loosely coupled integration and focus for security staff.
These kinds of distributed, intelligent, and autonomous abilities are essential as threats become more complex and working practices become more spread-out. According to Gartner, 89% of organizations want SASE and XDR to work together, either by consolidating into a single provider (43%) or keeping them distinct but integrated (46%). Keeping SASE and XDR distinct from one another enables a balance of best-of-breed functionality while maintaining loosely coupled integration and focus for security staff.
Whichever approach is taken, the argument for integrated security is clear. The next generation of cybersecurity is already here, and businesses are clearly stating their intent to implement SASE and XDR approaches, founded on integration. The days of point product portfolios are past: interconnection is king.