It is a cycle as old as cybersecurity itself. Attackers find a vector for compromise, defenders get wise and address it, attackers evolve and target a new weakness.
This is as true of social engineering and phishing, as it is of more technical attacks.
Business Email Compromise (BEC) was one of these evolutions itself. Tired of mass targeting employees with spam runs, targeted phishing attacks became popular as criminals learned from the tailored approaches taken by intelligence agencies.
Adapting this further, cyber attackers whittled down the targeting to an even finer point, spear-phishing the CEO on the assumption a high-value target has the most financial value.
Now, it seems a further evolution is on the horizon as research shows attackers have switched things up again.
Who are criminals targeting with Business Email Compromise attacks?
Perhaps driven by security teams and senior execs becoming wise to CEO fraud, threat actors have turned their sights on targeting finance teams, assuming this is the tip of the spear when it comes to achieving the ultimate aim – illicitly directing money out of companies.
The same research shows Business Email Compromise attacks targeted at finance teams are up a staggering 87%, with higher volume campaigns also taking root as efforts to compromise over 10 recipients at once increased by more than a quarter.
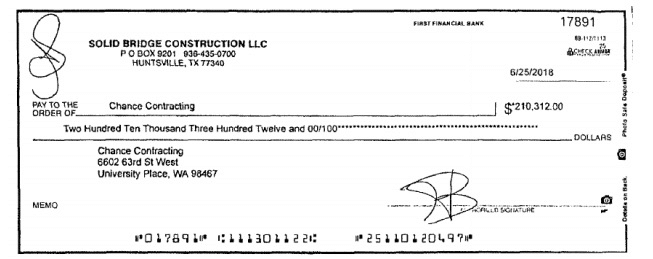
It also uncovers the scale of attempted attacks creeping up, with paycheck fraud decreasing and attackers focusing more on invoices, which as a recent court case showed, can potentially net criminals a huge windfall. See below for an example of just a single cheque that the criminals, in this case, managed to convince the finance team to part with.
How do I protect against Business Email Compromise fraud?
As always with a shifting threat landscape, it is important to understand how to evolve your security posture to reflect the new problem.
Training is crucial in helping to address the social engineering problem. Ultimately spear phishing takes advantage of human vulnerabilities and with people, education is the only patch. In this case, it seems clear that finance teams should be on the top of the list for regular, iterative phishing awareness training. There is a number of emerging technology platforms designed to teach employees to question emails more openly.
The human element should be backstopped with a contemporary email security solution which has been developed to address the more complex threat presented by Business Email Compromise. Only these technology platforms are capable of understanding the context of emails, which they do by analysing the vast number of data points required to extract meaning.
This means not only looking at email content, but also factors such as originating domain and IP addresses, as well as scanning for malicious links. Progressive variants of email security solutions also specifically designate rules for executives and subject them to stricter controls in an attempt to ring-fence decision makers. This will allow malicious emails to be quarantined or dropped, where necessary.
It is not only the mode of protection that is crucial in the contemporary threat landscape, but the location of protection. This means ensuring any email security solution chosen can be deployed in a wide range of cloud-based scenarios, such as Exchange Online within Microsoft Office 365, or even across multiple email service providers.
As BEC continues to evolve, security teams need to ensure they are continually matching the pace of the threat landscape. Social engineering is one of the major routes to compromise for any organisation, however, is often not re-evaluated as continually as traditional technology-borne countermeasures. For this reason, an iterative program of training is crucial.
This, underpinned with an email security solution which also continually evolves to stay relevant, is the best way to stay ahead of the changing nature of attackers.