Organisations have become reliant on the cloud to facilitate faster communication and collaboration between teams, but unfortunately, it comes at a price.
According to our recent report: Empowering the People, 65% of security professionals believe the cloud gives them less visibility and control of sensitive data.
With remote access here to stay, and as data regulation continues to tighten, organisations must consider whether their policies and technologies are fit for purpose today. Data security needs to be applied wherever the user is; across all communication, collaboration and storage tools.
How to avoid data loss: breaking bad habits
Since the dawn of the pandemic, there has been much debate around productivity and efficiency when working from home.
While productivity steals the spotlight, it’s important to acknowledge the potential for company security processes to fall by the wayside in this new working environment, leaving organisations vulnerable to data loss and leakage, and a host of cyberattacks.
Although the confidence and trust in cloud security providers is on the rise, user behaviour remains a major concern for businesses. As the boundaries between work and life become even more blurred over time, behaviours and bad habits filter across from personal life into the work environment. In our survey, 76% of the respondents reported employee behaviour in the cloud that could be putting their organisation at risk.
The most common risky behaviours included:
- using the same password for multiple accounts (41%)
- storing sensitive data in the cloud without the proper protection in place (33%)
- sharing links to documents in the cloud without authorisation (26%)
This ‘new normal’ we’ve found ourselves in has amplified the risk of unauthorised data sharing or data loss, not only major concerns but considerable threats to all businesses.
During this challenging period, in particular, the financial and reputational consequences of an attack could be catastrophic.
Tighten up data security with technology
While there is no doubt that education is a part of the solution, technology has to be the number one line of defence in avoiding data loss.
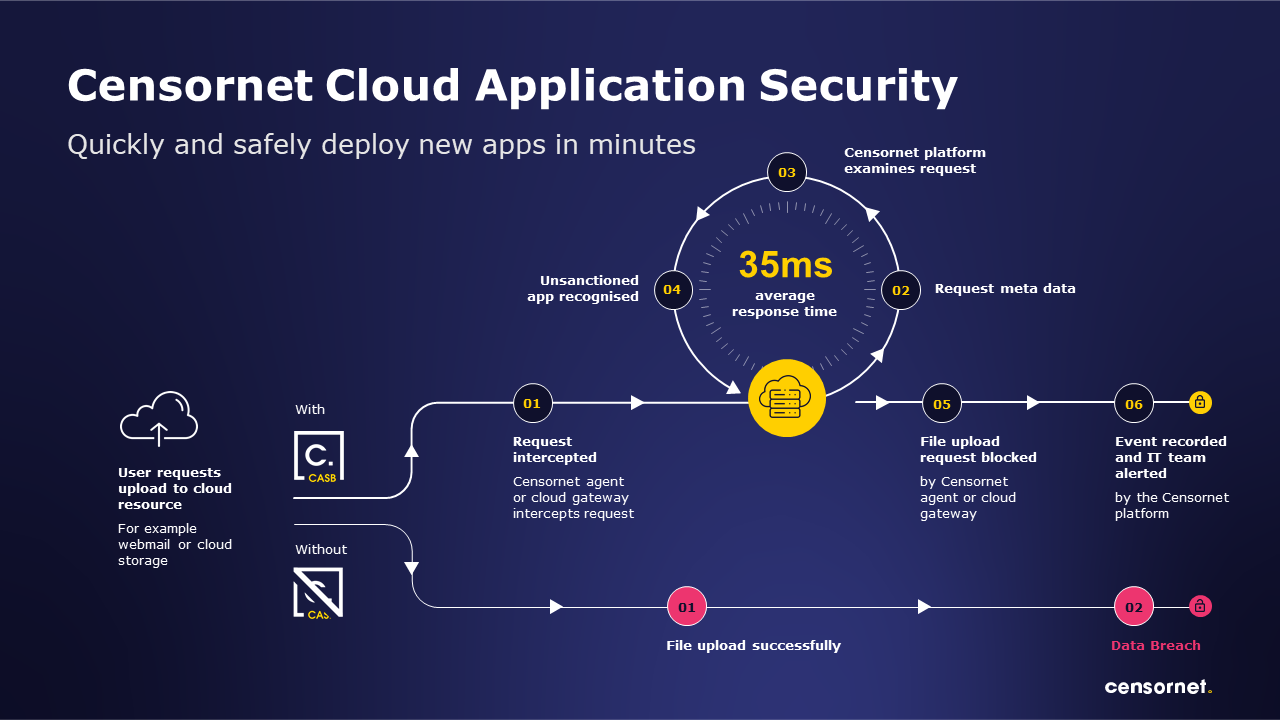
To wrestle back control of data stored in the cloud, organisations can deploy a Cloud Access Security Broker (CASB) solution that functions across all key business applications, such as Microsoft 365, Dropbox and Salesforce.
A CASB puts the security team back in the driving seat, providing them with full visibility and control to protect their organisation’s entire cloud infrastructure from one place.
From here, security professionals can implement policies to restrict access to and sharing of sensitive data and have granular insight into user activity – to see exactly when and where data is being handled inappropriately, and by whom.
Not only does this technology provide security teams with the information and tools required to identify individuals who need further cyber security training or even HR involvement, but it also satisfies the needs of the compliance team.
By implementing a CASB, the risk of data loss or a data security breach is reduced. This can be enhanced with the introduction of additional security, data loss prevention and image content analysis tools across cloud, web and email.
Lock out intruders
In addition to CASB, all organisations should implement context-aware or adaptive Multi-Factor Authentication (MFA), wherever possible, to address the ever-present issue surrounding account compromise.
With the majority of employees working remotely, and so many using the same password for multiple accounts, it is vital to question the context of the login.
Challenging users based on unusual behaviour such as a strange location, time, day, or device, will make sure the person accessing the account is who they say they are. Ensuring further verification before allowing access, particularly to business suites like Microsoft 365 or Google Workspace, protects not just data stored in the cloud, but unstructured data in email too.
Adaptive MFA uses numerous contextual variables to ensure users are not constantly challenged for passcodes.
Using existing phones or smartphones as the authenticator MFA is a relatively cheap and highly effective solution to roll out across an organisation, offering an extra layer of protection whether employees are in the office or elsewhere.
Don’t let remote working cloud your judgement
Now, anywhere-work environments are becoming the norm and the knee jerk ‘React’ phase is well behind us.
The next natural step is to take a risk assessment of the systems, services and data policies within the organisation, to expose any potential weaknesses and put the secure back in front of remote access.
In the race to provide a level of continuity as we entered lockdown 1.0, security understandably wasn’t the number one priority. Now that it is clear that the remote access provisions implemented are here to stay it’s time to ‘Review’ and ‘Recover’.
Taking back visibility and control of the cloud should be an empowering process for organisations, reaffirming processes and rules to prevent dangerous employee behaviour, and implementing additional layers of security around account access so staff can continue to work safely and unencumbered.
A risk assessment, followed by the implementation of appropriate, proportionate technical controls, combined with security education, will assure protection of sensitive information in the cloud – and businesses can thrive with all the benefits of remote working.
To find out more about how you can prevent data loss and other critical security challenges, download our full report: Empowering the People.