Ransomware is a growing threat that is a risk to organisations of every size.
From tiny one-person micro-businesses to global multi-nationals or even the critical national infrastructure which powers our civilisation, every business or institution is at risk of a cyber-attack.
The recent Colonial Pipeline hack in May 2021 is a reminder of the devastating power of ransomware.
During this incident, attackers infiltrated the systems of the company which provides almost half of the fuel which powers America’s East Coast. The hackers demanded $4 million in ransom. After first shutting down the pipeline, Colonial Pipeline paid up. Six days later, the pipes were back in action and the fuel was flowing again.
The incident prompted the White House to write to corporate executives, warning them to prepare for ransomware attacks.
“The most important takeaway from the recent spate of ransomware attacks on U.S., Irish, German and other organisations around the world, is that companies that view ransomware as a threat to their core business operations rather than a simple risk of data theft, will react and recover more effectively,” wrote Anne Neuberger, deputy national security adviser.
She added:” All organisations must recognise that no company is safe from being targeted by ransomware, regardless of size or location. We urge you to take ransomware crime seriously and ensure your corporate cyber defences match the threat.”
We couldn’t agree more. Censornet is dedicated to protecting customers from cyberthreats, so here is our advice on how to keep safe.
How To Protect Against Ransomware
Ensure your antivirus is up to date
The first step lies in ensuring your antivirus is up to date. This is a simple piece of advice, but one that people continue to forget.
Antivirus is not going to completely solve the problem – it is based on known signatures, so new types of malware (which are constantly being developed) will likely slip through the cracks. However, you don’t want to be caught out by known malware, and ensuring your AV is installed and updated across all endpoints works as an effective first line of defence against many ransomware strains.
Organisations also need to install the latest patches to fix system bugs and vulnerabilities. Failing to update means leaving your business open to cyber-attacks.
Educate to Protect
Educating your employees is crucial. They need to know how to recognise a phishing email and how to react if a suspicious message arrives in their inbox. Your business is your staff, and increased security knowledge will be a huge help in preventing you from falling victim to a ransomware attack.
As well as education, organisations should install email filters. One of the most common ways that ransomware reaches victims is through email phishing campaigns. While employee education is important, it can only go so far – sooner or later someone will slip up and click a dangerous link if the proper protections are not in place. To lower the risk of malware entering your organisation’s inbox and infiltrating your network, you should use software that blocks executable content. Stop these emails, and you will massively reduce the risk of a cyber-attack.
Secure Data
Data must also be locked down. Limit employee access to company data and dangerous online content.
Again, this is about reducing the opportunity for your employees to put your company at risk. Does everyone in your company have access to everything on your organisation’s system? If so, is that essential?
The weakest point in your network is human error because there is always one person who will accidentally click a phishing link or download a dangerous file. Limiting staff access will go a long way to reducing the threat surface.
Secure the Cloud
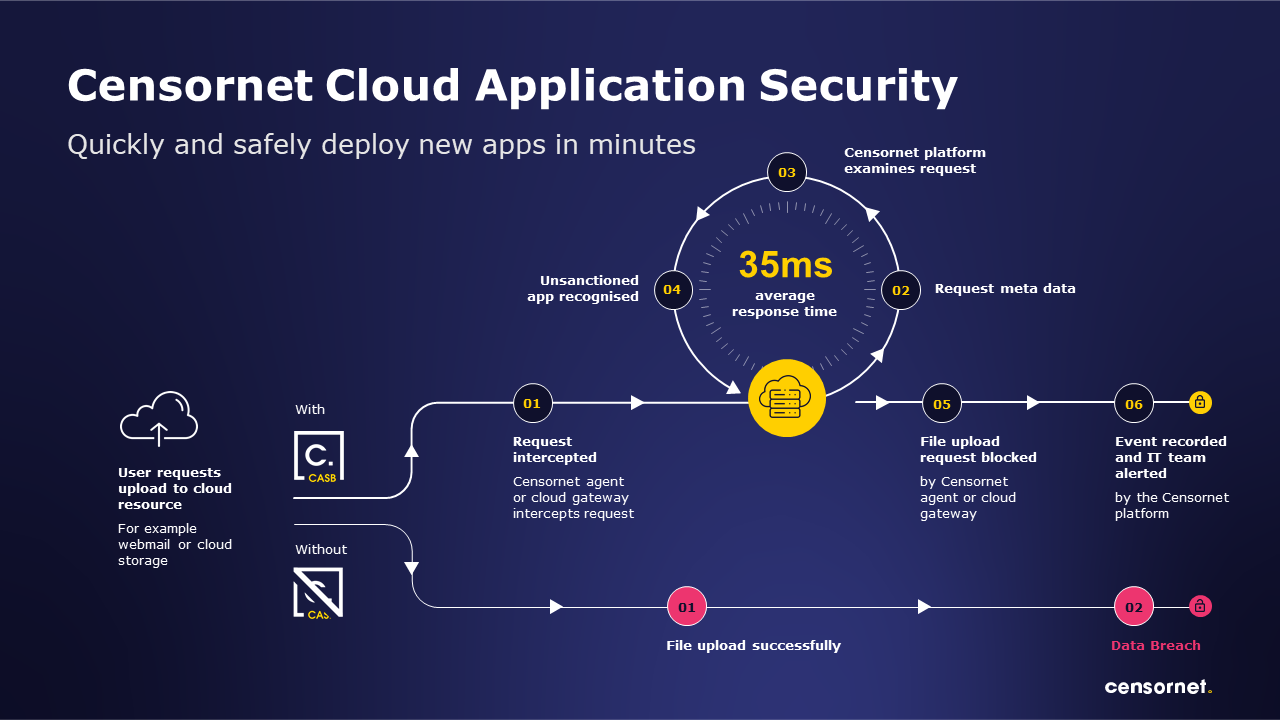
Organisations also need to ensure cloud applications are secured. In the age of remote or hybrid working, many businesses depend on cloud apps.
The average organisation uses 1,000 cloud applications and a vulnerability in just one could be a potential backdoor which allows ransomware to slip inside the network.
Cloud-only malware is on the rise. To combat this emerging threat, organisations need to establish visibility and control over their cloud applications and begin to treat it in the same way they would treat emails: scanning for malware and acting swiftly to quarantine threats.
Finally, it’s worth thinking about new models such as Zero Trust. The traditional safety of the corporate perimeter and its firewall are not sufficient to support a newly distributed workforce.
An entirely new perimeter built on identity and context is needed and prerequisite to the adoption of Zero Trust Network Access (ZTNA) – the first stop for many organisations on the journey to Secure Access Service Edge (SASE).
In an era where work is an activity, not a place, security needs to be available everywhere, all of time. Zero Trust makes sure that users authenticate first before being allowed into the network, whilst ZTNA powers this process.
Find out how Censornet can protect you in the era of hybrid working