Are your remote workers a target of social engineering with new COVID-19 scams? If your business has remote employees and uses email, the answer is probably yes.
Recent weeks have seen scammers switch their COVID-19 social engineering attack vector slightly, with a trend emerging for criminals to take advantage of the sudden popularity of remote meetings to phish the workforce.
A recent COVID-19 social engineering attack
On one occasion, employees were targeted with phishing links hidden inside calendar invites to attempt to try and bypass email gateways.
When clicked, the phishing URL itself heads to a document hosted on Microsoft SharePoint. Inside this document, is a further link to a malicious site hosted on Google seeking to collect sensitive data.
Attackers have also been busy targeting Microsoft 365 users with a similar phishing campaign designed to use the growth in Zoom calls to steal their login details.
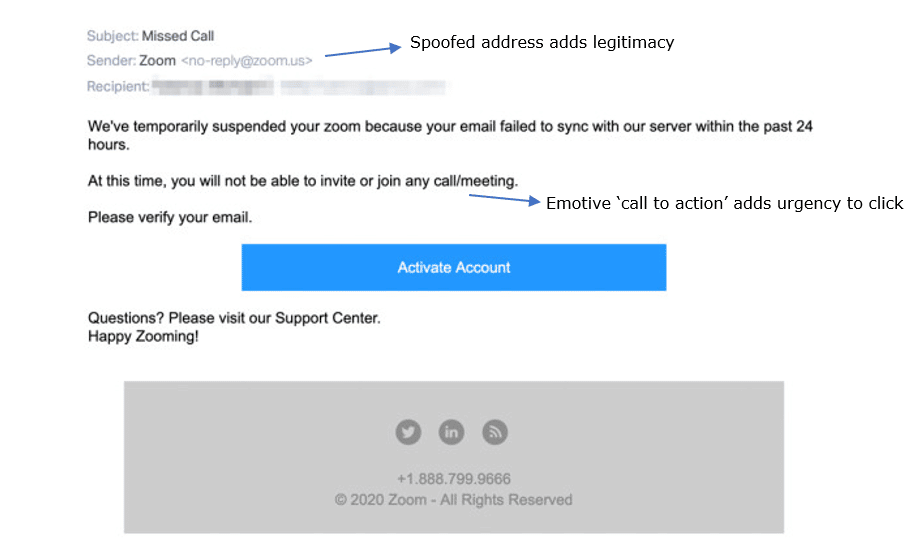
The social engineering attack sends a user notification of an alleged ‘Zoom account suspension’, spoofing the legitimate Zoom support address. Once clicked, it takes the unsuspecting user to a fake Microsoft 365 login page, asking for login details.
Both attacks go to prove that, as the world keeps changing, so will social engineering, most of which will be through phishing, but security teams should also keep an eye out for more outlandish attempts.
What do these COVID-19 scams mean for security teams?
The existence of COVID-19 cyber scams should not be news to security teams living in the new normal. However, this provides a strong example of the fact that attackers remain ruthless and, most importantly, creative and adaptable.
To counteract the human element of such scams, communication with employees is crucial to ensure they are aware of the latest phishing trends associated with the pandemic. These updated techniques should be communicated through existing internal communications channels, as well as built into an ongoing phishing training programme.
This should be underpinned with a progressive, multi-layered email security solution capable of analysing an array of message attributes and characteristics and understanding the context of communications to help companies stay relevant in a fast-moving threat landscape.
Such email security solutions make quarantine decisions based on nuanced content analysis, cross-referenced with markers such as originating domain and IP. This helps make qualitative decisions in examples such as this, where attackers are constantly evolving, and attacks are more targeted.
To protect senior decision-makers from more personalised scams, advanced email security can be tuned with custom rule-sets and also analyse multiple URLs beyond the original phish at time-of-click. This would have been particularly effective against the first example seen above, where a SharePoint document was used as a hopping off point to the real malicious landing page.
More advice on configuring your defensive email posture as the threat landscape continues to evolve can be found on our Defence365 hub and secure remote working page.